
Office of Compliance Programs
Information Security Training on Social Engineering
The Human Element of Information Security
Revised October 23, 2017
Introduction
Welcome to the LSUHSC’s Information Security training module on Social Engineering. It is intended for all personnel who have access to LSU’s computing resources and must be renewed on an annual basis.
Social Engineering is becoming the most common and most successful form of hacking. More and more, hackers are choosing to exploit human vulnerabilities rather than attempt to defeat a network’s technical defenses.
People are fooled every day by these scams because they haven't been adequately warned about social engineering techniques. Without the proper education, most people won't recognize a social engineer's techniques because they are designed to take advantage one’s natural tendency to be helpful. Awareness is the number one defensive measure so it is important that you stay up-to-date with your training.
What is Social Engineering?
Social Engineering, or “people hacking” is the process of deceiving people into giving away access or confidential information. It is the act of manipulating people into performing actions or divulging confidential information, rather than defeating technical defenses like breaching firewalls or cracking passwords. The term typically applies to trickery or deception for the purpose of information gathering, fraud, or computer system access; in most cases the attacker never comes face-to-face with the victim.
What You Need to Know
- How to recognize the most common social engineering techniques. Some examples include:
- Phishing Scams
- Telephone conversations (Vishing)
- Smishing
- Baiting
- Combination Attacks
- Hoaxes
- Shoulder Surfing
- Dumpster diving
- Physical access to your computer
- Insider Threats
- What steps to take when confronted with an attempt at social engineering.

Phishing Scams
Phishing is a technique to trick you in to taking action you would not ordinarily take (e.g. transferring funds or revealing your password). The hacker sends an email that pretends to be from a legitimate provider of services such as the IT department, HR department, a bank, a brokerage house, an ISP or an email service provider, etc.
In the message of the email, the hacker creates a sense of urgency or fear or other emotional response to motivate the reader to take the action (usually clicking on a link or opening an attachment) he desires.
If you suspect that an email may be a phishing scam, contact the purported sender, without using any links or other information from the email, and confirm the email is legitimate. For example, if the email says its from the IT department, call the Help Desk at 568-HELP.
If it is a phishing email, send it as an attachment using the "Attach Item" function in Outlook to spam@lsuhsc.edu, and delete it from your Inbox.
DO NOT click on any of the links or take any other action directed by the email until you confirm it is legitimate. A phishing message will direct you to take an action such as:
- Clicking on a link or an attachment
- Reveal your username and password
- Transfer funds
It will contain one or both of the following elements:
- Reason (“Due to the recent email upgrade. . .”)
- Consequence ( “. . . or your account will be suspended.”)
Milder messages may omit or imply the consequence: “Due to a lack of activity on your account (reason), you must click on the link below and login with your username and password (action).”
The loss of access to the account is implied.
More aggressive messages may omit the reason: “Funds must be transferred by clicking on the link below before COB today (action) or your payroll account will be overdrawn! (consequence)”
Any email that begins with EXTERNAL EMAIL: EVALUATE and asks you for your username and password or asks you to open an attachment should be considered a phishing email until proven otherwise.
Could it Be a Phishing Email?
- Is it unexpected? (i.e. There was no earlier email or other announcement letting you know to expect this message or the message is not part of the normal business routine.)
- Is the sender a title or department rather than an individual’s name? (e.g. from “Compliance Department” instead of "Roy Clay")
- Does it ask you to take an actions such as clicking on a link or an attachment, or transferring funds?
- Does it give a reason that makes the action seem logical?
- Does it ask for your username and password?
- Does it create a sense of fear or urgency or other emotional response by stating or implying dire consequences for failing to act (e.g. access suspended, account overdrawn, legal action taken, etc.)?
- Does the message start with "*EXTERNAL EMAIL: EVALUATE*"?
If the answer is “YES” to more than three (3) of the questions above, it may be a phishing email and you should send the email as an attachment (CTRL+ALT+F) to SPAM@lsuhsc.edu or contact your IT supporter for investigation. Do not, under any circumstances, use any of the links or rely on any information from an email you feel may be suspicious.
Actual Phishing Email
From: From: Human Resources (HumanResources@hr.securitydept.org) (Not a person)
Sent: Wednesday, January 18, 2017 11:14 AM
Subject: Important Update to Social Media Policy
*EXTERNAL EMAIL: EVALUATE* (Why is an email from HR coming from outside the network?)
LSU Health Sciences Center New Orleans is instituting new social media policies for all faculty and staff. Due to recent events in the news we are going to start blocking many of the popular social media sites for employees who do not need them for justified, business purposes.(reason)
We need your help to determine if you utilize social media and how you feel about this policy change. We have created a portal page on our internal network to get each employees usage of social media so we can determine which policy should be applied to your workstation. Please visit the Portal Page www.hrsecuritydept.org and complete this survey.(action)
Your participation is mandatory and this survey must be completed in the next five business days so we can compile results before the default block policy is applied.(consequence)
Thank you
Social Media Compliance Team (Not a person)
Does It Meet The Test?
- The sender is not a person.
- It asks you to take action.
- It asks you to go to a web page (Portal Page) that asks for your username and password.
- It provides a reason (new policy) that makes the request seem logical.
- It implies you will be blocked if you don't comply. (consequence)
It has five of the characteristics of a phishing email listed above.
Legitimate Email from LSUHSC
From: Bettina Owens - Asst Vice Chancellor for Information Technology
Sent: Thursday, July 07, 2016 2:30 PM
To: LSUHSC N.O. Faculty, Staff and Students
Subject: Email Scams
LSUHSC is currently experiencing an increase in Phishing emails and an increase in people succumbing to these emails by providing the perpetrators with their LSUHSC credentials. Responding to a Phishing email places all of LSUHSC in jeopardy.
Phishing emails attempt to trick individuals into divulging their user IDs,passwords, social security numbers, etc. If you are in doubt whether an email is a phishing email please send the email as an attachment (CTRL+ALT+F) to SPAM@lsuhsc.edu or contact your IT supporter for investigation.
Guidelines on phishing:
- We don’t know your password and don’t need to know it to get our job done. We or any legitimate site would never ask for it, especially in response to an email.
- Be very suspicious of requests to verify your account or mailbox for any reason, particularly due to exceeding limits or preventing deactivation. LSUHSC IT knows owner and access information and does not need to ask you this in an email.
- Never divulge your SSN, bank account, or other such sensitive information via an email. LSUHSC-NO already has all the information needed for administrative purposes. Legitimate sites will not ask for this information via email.
- Be suspicious of any email asking you to click on a link. Clicking on a link could install malware on your computer to be used by the perpetrator to gain access to the LSUHSC network.
- Hover your cursor over all links in the email to determine if any of the URLs go to a web address other than the proposed sender’s site before clicking on the link.
Thanks to all who picked up that this was a phishing email and took the time to let us know about it.
*********************************************
This message has been authorized by LSU Health Sciences Center administration for mass distribution as a service to our faculty, staff, and students.
Is this a Phishing Scam? (Yes or No)
From: Maddox, Amy Marie [mailto:amaddo@tbh.net]
Sent: Monday, February 06, 2017 10:06 AM
Subject: Important Message From HR Department
*EXTERNAL EMAIL: EVALUATE*
To All Faculty\Staff
Hi, a private document has been sent to you by the Human Resources Department
Click Here to Log into Employee Self Service to view the document now.
HR Department

YES!!
From: Maddox, Amy Marie [mailto:amaddo@tbh.net]
Sent: Monday, February 06, 2017 10:06 AM
To All Faculty\Staff
Subject: Important Message From HR Department
*EXTERNAL EMAIL: EVALUATE* (Email is from outside the LSUHSC campus)
Hi, a private (sense of urgency) document has been sent to you by the Human Resources Department
Click Here to Log into Employee Self Service(Action) to view the document now.(More urgency!)
HR Department (Not a person)

Also, note the date. February 6th is just a few days after the deadline for sending W-2 forms to employees. This may be a scam to get your tax information in order to file a fraudulent return.
What Do I Do?
- With the suspicious email open, press CTRL-ALT-F.
- A new email will open with the suspicious email as an attachment.
- Type "spam@lsuhsc.edu" in the To: address field of the new email.
- Click "Send".
Is this a Phishing Scam? (Yes or No)
From: IT Helpdesk[helpdesk@lsuhsc.com.ru]
Sent: Monday, September 26, 2016 8:45 AM
To: {Recipient List Suppressed}
Subject: Irregular Account Activity
*EXTERNAL EMAIL: EVALUATE*
Our system has detected irregular activity on your account. Taking precautions, certain limitations and measures have been placed on your account in accordance of the User Agreement and Privacy Policy.
To regain access without any interruption to your account, please visit the following link to our Security Customer Support Center to help you re-validate your account activity and keep your account safe from potential risk.
www.lsuhsc.helpdesk.com.ru
Please read the entire page and follow all directions to validate your account.
Thanks for your cooperation.
IT Helpdesk

YES!!
From: IT Helpdesk (Not a person) [helpdesk@lsuhsc.com.ru]
Sent: Monday, September 26, 2016 8:45 AM
To: {Recipient List Suppressed}(Must be serious!)
Subject: Irregular (It is serious!) Account Activity
*EXTERNAL EMAIL: EVALUATE* Email is from outside the LSUHSC campus
Our system has detected irregular activity on your account.(reason) Taking precautions, certain limitations and measures have been placed on your account (consequence) in accordance of the User Agreement and Privacy Policy.
To regain access without any interruption to your account, please visit the following link (action) to our Security Customer Support Center to help you re-validate your account activity and keep your account safe from potential risk.
www.lsuhsc.helpdesk.com.ru
Please read the entire page and follow all directions to validate your account.
Thanks for your cooperation.
IT Helpdesk (Not a person)

What Do I Do?
- With the suspicious email open, press CTRL-ALT-F.
- A new email will open with the suspicious email as an attachment.
- Type "spam@lsuhsc.edu" in the To: address field of the new email.
- Click "Send".
Phishing Season
While anyone can receive a phishing email at any time, there are certain times where phishing is more active. These include:
- As was noted above, the month of February. Companies provide employees with tax information by January 31st of each year. Hackers attempt to access that information by sending out phishing emails purporting to be from the "HR Department" in order to file fraudulent tax returns.
- In the aftermath of a disaster. Hackers will send emails purporting to be from a disaster relief organization seeking donations in order to collect financial information (e.g. credit and debit card numbers, bank account information, etc.)
Things to Remember
LSUHSC-NO will NEVER ask for your user name or password in an email.
If it is an email sent to all employees and/or students, it will contain the sender’s name and job title and the following text will be appended to the end of the message: “This message has been authorized by LSU Health Sciences Center administration for mass distribution as a service to our faculty, staff and students.”
Emails from outside the LSUHSC network will contain the message “*EXTERNAL EMAIL: EVALUATE*” NEVER provide your username or password in response to an email from outside the LSUHSC network.
Be especially wary of any unexpected email that arrives after the first of the year or after a well publicized disaster. It could very well be a phishing email.
If you’re not sure whether an email is a phishing scam or not, independently confirm the email by contacting the sender without using any information in the email. Obtain information from your own contact list or from the sender’s website.
Send all suspected phishing emails as an attachment to spam@lsuhsc.edu, and
delete them from your Inbox.
Telephone Conversations (Vishing)
Often hackers will simply call the intended victim and persuade them to take a desired action. This is often called “voice phishing” or “vishing”.
A hacker might impersonate a Help Desk supporter or a computer vendor such as Microsoft during a phone conversation in an attempt to:
- Get you to reveal your username and password.
- Run a program or change the configuration of your computer to give him access.
Other variations include:
- An email claiming to be from the IRS or other government agency announcing a serious problem and providing a phone number to call.
- A window pops up while browsing the the Internet that warns of dire virus infections. The message instructs you to call the number provided to "remove" the infections. (There are always more than one.)
Passwords should NEVER be given out during a telephone conversation.
Computer vendors will NOT call users directly.
- If someone calls claiming to be a vendor, tell them to contact Computer Services and explain the problem.
- Do not, under any circumstances, follow any instructions given to you by this person, no matter what dire consequences they may describe.
- Hang up as quickly as possible and report the call to the Help Desk at 568-4357.
The Help Desk will ask for a secondary form of authentication when unlocking your account or resetting your password such as:
- Last four digits of your Social Security number
- Date of birth
- Place of birth

You Get a Call at Your Desk . . .
The caller gives his name and states he works for MicroSoft Corp. He is calling you because he is getting numerous alerts from your computer indicating your computer is infected with multiple viruses. Your computer is working fine as far as you can tell. He wants you to carry out a series of steps to correct the problem.
What Should You Do?
- Hang up on the caller and continue working. No big deal.
- Follow the caller’s instructions. Virus infections are very serious and the caller said he was from MicroSoft so he must know what he is doing.
- Hang up and call the Help Desk (4357) to report a phishing call.
You Should:
Hang up and call the Help Desk to report a phishing call.
- An employee of a computer vendor (e.g. MicroSoft, Cisco, HP, etc.) will never call an individual user.
- NEVER perform steps on your computer at someone’s direction unless you have called that individual first (e.g. the Help Desk) and asked for help.

Smishing
“Smishing” or “SMS phishing “is similar to phishing except the communication is sent via text messaging.
Criminals set up an automated dialing system to text or call people in a particular region or area code (or sometimes they use stolen customer phone numbers from banks or credit unions).
The victims receive a message designed to trick them into installing malware or revealing financial or other sensitive information.
Armed with access to the victim’s phone or information revealed by the victim, criminals can steal from victims’ bank accounts, charge purchases on their charge cards, create a phony ATM card, etc.
Because of the similarities betweens texts and emails, smishing techniques are similar to phishing techniques. When ever your receive a text you should ask youself the following questions:
- Is it unexpected? (i.e. There was no earlier email or communication letting you know to expect this message or the message is not part of the normal routine.)
- Is the sender someone who is NOT in your address book?
- Does it ask you to take an action such as clicking on a link?
- Does it give a reason that makes the action seem logical?
- Does it ask for your username and password?
- Does it create a sense of fear or urgency or other emotional response by stating or implying dire consequences for failing to act (e.g. access suspended, account overdrawn, legal action taken, etc.)?
If the answer is “YES” to more than three (3) of the questions above, it may be a smishing text.
Smishing Examples
You receive the following text:
“Dear Walmart shopper, Congratulations you have just won a $1000 Walmart Gift Card. Click here to claim your gift. www.fraudulentwebsiteaddress.com “
Once you click on the link, you are asked a number of personally identifying questions “for verification purposes” culminating in a request for your credit card number.
Once you provide that information, the smishers have everything they need to steal your identity.
In July 2016 many iPhone users received the following text:
“Apple Store
Your account is on the verge of closure!
We have recently determined that more computer are connected to your
account and multiple password failures were present before access.
Now you need to re-confirm your account information to us..
If this is not done within 48 hours, we will be forced to suspend your
account,
To confirm your Apple ID safely, click on the link below:
Click here to unlock your Apple ID
www.apple.com
Failing to do so until the 28/07/2016 will be considered a denial of
our terms and conditions and your account will be permanently closed.”
When users clicked on the link and supplied their Apple ID and password, their accounts were stolen.
Hackers have been using SMS messages to trick users into loading malware on their Android phones.
The victim receives a text:
“You have received a multimedia message from +[01] [555-555-5555] Follow the link http://www.mmsforyou.net/mms.apk to view the message”
Clicking on the link downloads the malware which gives the hacker complete control of the phone.
The hacker can monitor the victim’s location, eavesdrop on conversations, steal passwords, activate the phone’s camera, etc.
Smishing Prevention
- Don’t respond to text messages or automated voice messages from unknown or blocked numbers on your mobile phone.
- Treat your mobile phone like you would your computer…don’t download anything unless you trust the source.
- When buying online, use a legitimate payment service and always use a credit card (not a debit card) because charges can be disputed if you don’t receive what you ordered or find unauthorized charges on your card.
- Don’t respond to unsolicited texts or phone calls requesting personal information, and never click on links or attachments contained within unsolicited texts.
Baiting
Baiting is similar to phishing except that instead of providing a reason or consequence, victims are led to believe they will receive some sort of benefit.
Email Baiting
The simplest form of baiting is to send an email with a subject line designed to pique your curiosity enough to get you to click on the link or attachment.
- Celebrity pictures or scandals (“HOT PICS of [name of celebrity].”)
- Breaking news (“LATEST INFO on flood insurance, Affordable Care Act, etc.)
- Offers for “free” or “discounted” software.
- Unbelievable bargains (Cruises, iPads, etc.)
- Attachments claiming to be invoices or lawsuits.
- Charity scams (“Aid the victims of the Hurricane Maria.”)
- Offers of “exclusive access” if you simply login with your email credentials.
- Online surveys.
- Emails claiming to be from the IRS or FBI.
Don’t click on these links in unsolicited emails or text messages. Instead, send all such emails to spam@lsuhsc.edu.
Media Baiting
Another variation of baiting involves leaving various types of computer media (CDs, DVDs, USB drives, SD cards, etc.) where prospective victims will find it.
The media are labeled with something designed to pique the victim’s curiosity like “Executive salary report” or “Wet T-Shirt Video”.
The media actually contain malware that will install itself when it is plugged in the victim’s computer.
The malware gives the hacker complete control over the victim’s computer.
In a study by the University of Illinois, researchers left 300 USB drives in and around the Urbana-Champaign campus.
- The drives had various labels like “final exam solutions”, “confidential”, or “Pictures-Winter Break”.
- 98% of the drives were picked up.
- 45% of the drives were plugged into a computer and the files were opened.
- One of the drives was plugged into a computer less than six (6) minutes after it was left by the researchers.
As part of a security audit, employees were mailed a USB drive along with a letter stating that an update to the company’s anti-virus software was needed and gave the employees instructions on how to plug in the USB drive and run the “update”.
The “update” was a malware program which gave the auditors the access they were seeking.
Baiting Prevention
- Never plug anything into your computer unless you know where it has been.
- Disable “Auto-Play” on your computer.
- Ensure you have anti-virus software with up-to-date virus definitions installed on your computer.
- LSUHSC-NO does all software updates through the network. There is never a need to plug in a USB drive.
Combination Attacks
Recently, hackers have been combining different social engineering attacks. One example is called Franco-phoning.
- Franco-phoning combines a phishing email with a telephone call to convince the victim to turn over sensitive data or install malware.
- First, the hacker carefully researches the target organization to obtain names of executives, their assistants, customers, phone numbers, and email addresses.
- Using that information, the hacker calls a targeted individual within the organization, usually an accountant or an administrative assistant with authority to make large financial transactions.
- The hacker poses as a customer, bank representative or another employee using a real name based on his research.
- The hacker provides a plausible story, again using his research, and requests the assistance of the victim.
- The hacker then sends an email with an attachment that is supposed to be an invoice or wire transfer that needs immediate processing.
- When the victim clicks on the attachment, malware is installed on the victim’s computer that allows the hacker to assume the victim’s logon ID and executes transfers of large sums of money.
- Unlike other phishing attacks, franco-phoning emails have perfect grammar and spelling.
- Because of the research the hacker does, special formats and messages are usually correct.
In April 2013, the administrative assistant to a vice president at a French-based multinational company received an email referencing an invoice hosted on a popular file sharing service. A few minutes later, the same administrative assistant received a phone call from another vice president within the company, instructing her to examine and process the invoice. The vice president spoke with authority and used perfect French. However, the invoice was a fake and the vice president who called her was an attacker.
The supposed invoice was actually a Trojan that was configured to contact a command-and-control (C&C) server located in Ukraine. Using the Trojan, the attacker immediately took control of the administrative assistant’s infected computer. They logged keystrokes, viewed the desktop, and browsed and copied files.
The best defense is to independently verify everything before taking action on any request that seems out of the ordinary. Always ask yourself two questions:
- What damage could be done if I help this person and they turn out to be a scammer?
- How can I independently verify what this person is saying?
If the caller claims to be from IT, call IT on a separate line and verify what the caller says. If the caller claims to be from your bank, call your regular banker to verify what you are being told.
Hoaxes
One type of suspicious email is the hoax. It warns of a virus or other type of malware that will cause serious harm to your computer such as wiping the hard drive. It is especially perfidious because it usually comes from a well-meaning friend or relative who has been duped by the hoax.
Hoax emails generally have the following characteristics:
- They are sent by a friend or colleague.
- They warn of a “new” virus, malware or hazard.
- They claim that this new hazard damages your computer in some catastrophic way, usually erasing the hard drive.
- The email claims that anti-virus programs are unable to detect it or have been caught off guard by its appearance.
- It urges you to send this “warning” to everyone in your address list.
Problems Caused by Hoaxes
The main problem caused by Hoaxes is that they overload email systems with unnecessary traffic.
In addition, those that follow the instructions in the Hoax email wind up disabling their computers and must have them repaired or reconfigured before they are usable again.
As with other threats, Hoaxes have developed variations. Some variants to watch out for are:
- The virus named in the hoax is the name of an actual virus. However, the real virus acts differently than what the hoax describes.
- The hoax will instruct recipients to delete an obscure system file causing their computers to malfunction on the next boot-up.
How Can You Tell if it is a Hoax?
How do you determine whether a message is genuine or a hoax?
- Does the message have three or more of the characteristics of a hoax?
- Remember that any links in the message are there to convince you of its authenticity so don’t rely on them.
- Enter specific or unique terms from the message into an Internet search engine and see if any references to hoaxes come up.
- Call the Help Desk.
You can check the following websites:
It is a violation of CM-42 to re-transmit virus hoaxes.
Shoulder Surfing

Hackers could attempt to learn your password or breach confidential information by:
- Watching while you type your pass.
- Reading your computer’s screen.
Prevention:
- Type your password quickly or when no one else is watching.
- Position your screen so it can’t be easily viewed by someone behind you.
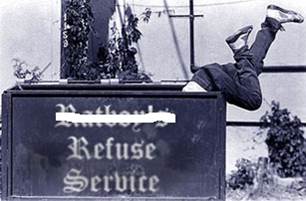
Dumpster Diving
A hacker might learn information by:
- scouring trash for passwords written on scraps of paper
- reading documented computing procedures
- finding discarded hard drives, discs, or CDs
Destroy all information in accordance with PM-36 once it is no longer needed.
Contact your local computer supporter or the Help Desk for assistance with properly erasing or destroying computer media.

Physical Access to your Computer
Physical access to a computer is the ultimate access a hacker can obtain.
A hacker could access, remove, destroy, or otherwise damage your computer.
Once the hacker has removed the computer, he has all the time he needs to crack passwords, obtain encryption keys
Prevention: Always use good physical security measures to prevent theft or damage to your computer.
- Lock your office when you leave for lunch or breaks.
- Keep your laptop in the trunk of your car, not on the seat.
- Set an idle timeout that automatically locks your screen and keyboard if the computer is not being used.
- Encrypt the hard drive to prevent access to your data in the event the computer is stolen
- Consider obtaining a hardened laptop case, (based on cases used to transport firearms) for storing a laptop when not in use.
- Don’t use the “sleep” or “hibernate” functions on your computer. Shut it down when not in use.

Tailgating or Piggybacking
- Another way to gain physical access is to follow someone after they have unlocked a door.
- Never unlock a door for someone you don’t know.
- Never allow someone to follow through a locked door.
- If someone attempts to follow you, stop them and ask, politely but firmly, if you can direct them where they need to be.
Threats from Insiders
Few things generate as visceral a sense of biliousness as the thought that a member of our LSUHSC-NO community would break the trust of their patients, students and coworkers. But, as the stories below demonstrate, the possibility exists.
Man Found Guilty of Selling Stolen Patient Info Used to File False Tax Returns
Jean Baptiste Alvarez (a/k/a Alex) of Pennsylvania was found guilty in 2016 of conspiracy to defraud the United States with respect to false claims, aggravated identity theft and misuse of social security numbers. According to evidence presented at trial, Alvarez unlawfully provided to Peterson Rene and Marc Celestin, who is charged separately, the personal identifying information (PII) of hundreds of real persons.
Alvarez used his job as a technician at a West Philadelphia mental health clinic called Kirkbride Center to obtain and smuggle out patient information. That patient information was taken from census sheets at the clinic and included patient names, Social Security numbers and dates of birth. Alvarez then sold the information for up to $1,000 per page; that information was subsequently used to file fake tax returns.In total, Alvarez was charged with disclosing and using the Social Security numbers and PII of approximately 183 persons.
Former Ascension Parish Health Unit employee pleads guilty to stealing, selling patient SSNs
In 2015, Ta'sha Thomas pled guilty to gaining access to patient information in the health unit's database, taking the information and selling it to another person, Mona Hill, who used the information to file fraudulent federal tax returns. Ms. Hill paid Ms. Thomas between $8,000 and $9,000 for the stolen information. Additionally, Ms. Hill received more than $400,000 from the fraudulent returns. She has been separately prosecuted and convicted.
Alverez and Thomas were not hackers gaining access to information from a remote location. They worked in the facilities they pillaged. As they were stealing from their patients, they were sitting next to coworkers who were doing their best to serve those same patients.
But what about those coworkers? Did they notice anything?
We must all be on the alert for behaviors that might be indicators of an insider threat. Knowing the safeguards that must be applied to handling information, report behaviors such as:
- Mishandling or misusing protected or restricted information.
- Moving protected or restricted information from premises for unauthorized, personal, or unknown reasons.
- Copying protected or restricted information unnecessarily.
- Establishing unauthorized means of access to university information systems.
- Seeking access to protected or restricted information on subjects not related to job duties.
- Sudden reversal of financial situation or repayment of large debts or loans.
If you observe any of these behaviors or suspicious behaviors by an individual, report the activity to your supervisor or the Office of Compliance Programs.
While not all suspicious behaviors or circumstances represent a threat, each situation must be examined along with information from other sources to determine whether or not there is a risk. Observing even a single activity and not reporting it can increase the potential damage that can be done.

Incident Reporting
Notify your local computer supporter or the Help Desk if:
- You suspect your password has been compromised.
- You suspect your files have been tampered with.
- Your computer behaves abnormally.
- You suspect someone has obtained or is trying to obtain unauthorized access.
- A device or media with protected or restricted information has been lost or stolen.
- You have been called by someone claiming to be a vendor.
Remember
Social engineering hackers work very hard to make their scams appear legitimate.
Sooner or later, everyone will be fooled by a social engineering scheme. If you are fooled, you probably won’t remember it because it appeared to be no different than hundreds of other legitimate issues you have addressed as part of your duties.
Simply take whatever corrective action is required. (changing passwords, repeating training, etc.)
Getting Help
If you have any questions, please contact the Office of Compliance Programs by:
- Email: nocompliance@lsuhsc.edu
- Phone: 504-568-5135
- In Person: RCB, suite 807
- Website